A Simple Collaborative Method in Web Proxy Access Control for Supporting Complex Authentication Mechanisms
![Hybrid rule-based botnet detection approach using machine learning for analysing DNS traffic [PeerJ] Hybrid rule-based botnet detection approach using machine learning for analysing DNS traffic [PeerJ]](https://dfzljdn9uc3pi.cloudfront.net/2021/cs-640/1/table-3.png)
Hybrid rule-based botnet detection approach using machine learning for analysing DNS traffic [PeerJ]
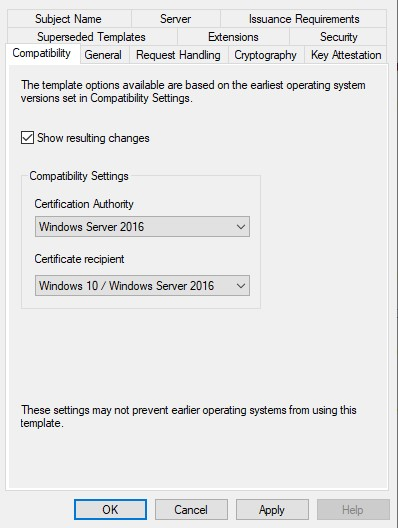
Cannot select Windows Server 2016 CA-compatible certificate templates from Windows Server 2016 or later-based CAs or CEP servers - Windows Server | Microsoft Learn
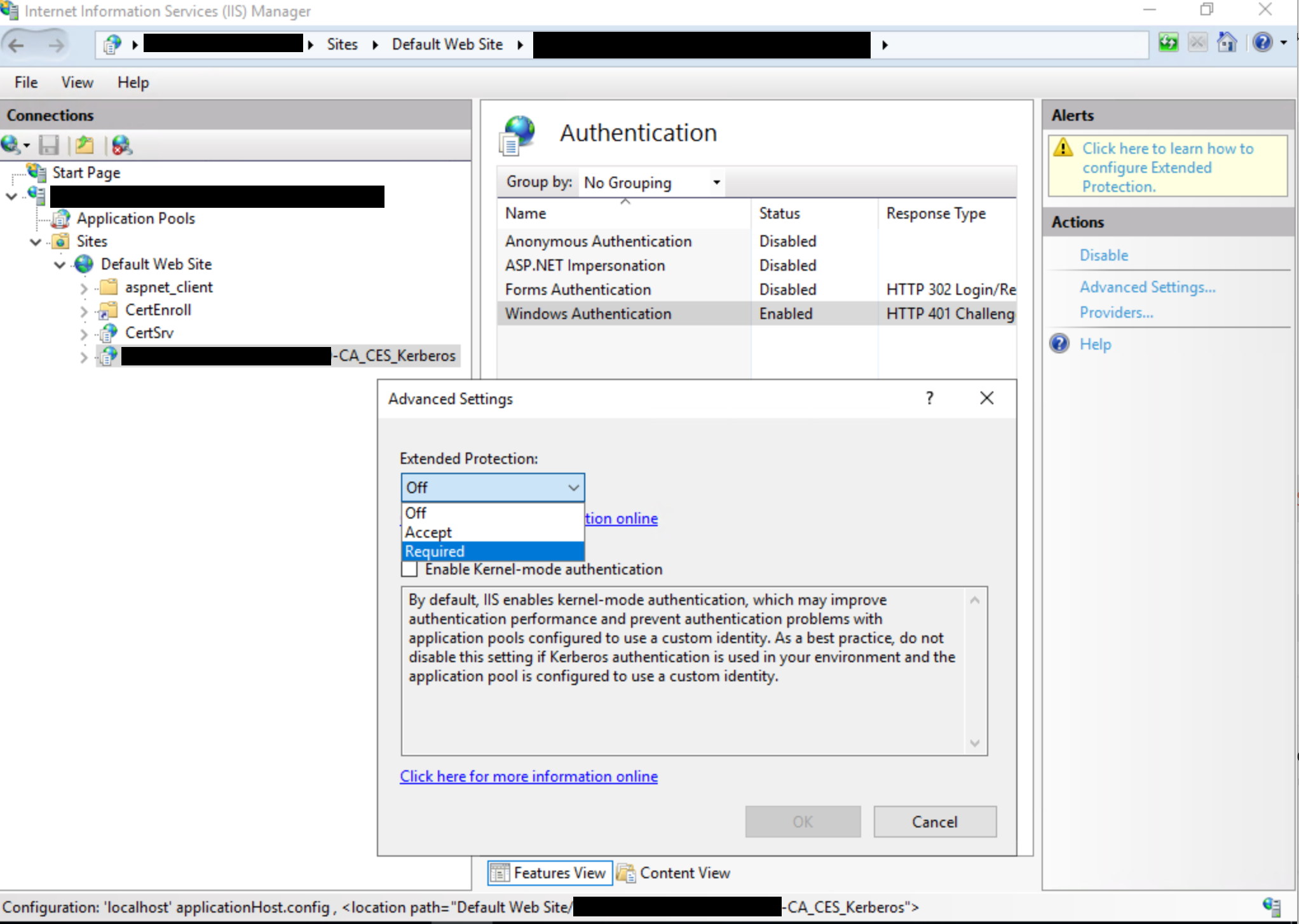
KB5005413: Mitigating NTLM Relay Attacks on Active Directory Certificate Services (AD CS) - Microsoft Support










![What is a Security Operations Center? [SOC Security Guide] What is a Security Operations Center? [SOC Security Guide]](https://www.crowdstrike.com/wp-content/uploads/2022/03/cs-101-active-directory-security.jpg)